Meltdown, Spectre, Will Change the Way Chips are Designed, Researchers Say
The security design flaws revealed last week, can potentially enable hackers to glean passwords entered by users in real-time
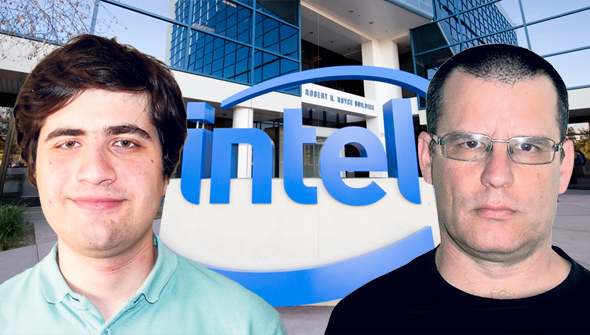
The backlash that followed the publication of security flaws in chips by Intel and AMD will result in a shift in the way chips are designed, according to Daniel Genkin, one of the researchers who contributed to the research. In an interview with Calcalist held Friday, Mr. Genkin, a postdoctoral fellow at the University of Pennsylvania and University of Maryland, said he expects the case to become part of chip design curriculum.
For daily updates, subscribe to our newsletter by clicking here.
Last week, a large team of Google security researchers published details of two separate security flaws affecting a wide range of central processing units, also known as chips, which render them especially vulnerable to hacking attempts. Dubbed “Meltdown” and “Spectre,” the flaws found affect PCs, smartphones, tablets and servers powered by chips by Intel, AMD, and chips, including ARM designs.
The flaws were first discovered last year by Google's Project Zero, a team of security analysts working for Google’s parent company Alphabet Inc., and also by an independent team of university researchers. Both teams approached electronics companies in order to address the flaws found before publication. Google's researchers came forward with the information ahead of the originally coordinated disclosure date of January 9 in response to public reports and speculation in both the press and the security community.
On Thursday, Apple announced that all its devices are affected by the flaws except Macs using the latest version of macOS and the latest iOS, version 11.2.
Microsoft, Apple, and Linux, which are the three main operating system makers, have all started rolling out patches, and Amazon also said its vulnerable to the flaws found.
On Wednesday, Google said Android phones updated with the latest security updates are safe, as are web services like Gmail.
On Wednesday, Intel said it believes the security flaws do not have the potential to enable the corruption, modification or deletion of data in a blog post.
Yuval Yarom, a senior lecturer at the University of Adelaide, Australia, and Mr. Genkin, were part of the team that discovered the flaws independently of Google. The two have been working together in the domain for the past five years.
“What we see here is the pinnacle of attacks on processors, the impact is different and much larger than other breaches, and so patching the situation is much more complicated," said Mr. Genkin in a phone interview with Calcalist Friday.
He believes the exposure of these flaws will fundamentally change the perception of what is considered good processor design. "Once the panic is over, we hope the relevant engineers will learn the lesson and stop doing things like everyone used to."
In a phone interview the same day, Mr. Yarom added that the design flaws are unprecedented not just because they are hardwired but also because of the nature of data they enable hackers to access, in a relatively easy way.
The breach enabled the researchers to find saved passwords, for example, and read emails in real-time. "While the user is typing a login password for Facebook, we can receive it," Mr. Yarom said. "The same goes for (passwords typed for) bank services and other similar services."



