Survey: Cybersecurity executives see increase in attempted credential theft
The survey, conducted by CyberArk, found that the most at-risk group facing the highest number of increased attacks are end-users, or those business users with access to sensitive data
16:3711.04.21
A recent survey by Israeli company CyberArk, a leader in identity securityת discovered that some 97% of senior security executives believe that attackers are increasingly aiming to steal their corporate credentials. As organizations migrate their assets to protected cloud networks, and increase third-party access to their resources, enabling remote work models, weak points are being discovered in corporate networks which may not be fully protected.
The CyberArk report titled “The CISO View 2021 Survey: Zero Trust and Privileged Access,” showed that there is growing concern among senior executives and those in the cybersecurity industry that cyberspace is becoming less safe, and there is an urgency to secure and protect access to corporate networks. CyberArk is mainly concerned with limiting access management and provides comprehensive security offerings for distributed workforces and hybrid-cloud workloads, helping secure and ensure corporations’ most crucial assets.
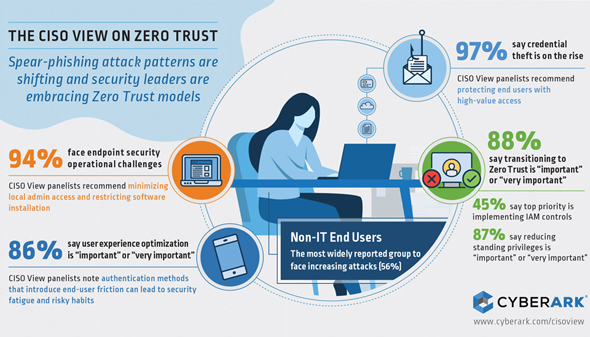
An infographic showing the results of the survey. Photo: CyberArkCYBERARK
The survey found that the most at-risk group facing the highest number of increased attacks are end-users, or those business users with access to sensitive data. Some 56% of respondents found that such people were victims of cyberattacks. That was true for those in senior leadership positions (48%), third-party vendors and contractors (39%), and DevOps and cloud engineers (33%). Credential theft attempt for personal data was also on the rise (70%) and on financial systems and data as well (66%). This highlights attackers’ interest in gaining access to highly sensitive systems that are often held by end-users rather than administrators.
In response to those disturbing data figures, security leaders are interested in adopting a Zero Trust approach wherein cybersecurity is beefed up, recognizing that trust is a vulnerability which must be limited. Some 88% of respondents polled believed that adopting such an approach is “very important” or “important.” To implement such a model, a top priority would be to focus on Identity and Access Management, which was chosen by 45% of respondents as “important.” Other types of controls were also favored by respondents, and just-in-time access controls were chosen by 87% of respondents who believed that limited standing privileges is an “important” or “very important” aspect of Zero Trust.
Since hackers are able to exploit weaknesses, there is a growing need for security solutions that work despite internal constraints. Around 94% of respondents said endpoint security is “important,” with 46% saying that installing such software on networks is challenging. Also, 86% were concerned about harming user experience optimization, saying it was “important” or “very important,” but highlighted the need for security tools and policies to not be bypassed or simply ignored due to lax behavior.
“Reverberations from the SolarWinds attack continue to underscore the need to protect privileged credentials and break the attack chain to organizations’ most valuable assets,” said Mike O’Malley, who serves as the Senior Vice President of Global Marketing at CyberArk. “As new identities multiply across the enterprise, this survey emphasizes the importance of a Zero Trust-based approach to Identity Security. For security leaders seeking to mitigate the risks of spear-phishing, impersonation attacks and other forms of compromise, we believe the peer experiences captured in the CISO View reports will serve as an invaluable tool, no matter where their organization is on the Zero Trust maturity-curve.”
The survey was part of the fifth in the CISO View series, and was based off of in-depth interviews with 12 top security executives from Global 1000 companies conducted during the fourth quarter of 2020. The CISO View series was created with assistance from the independent research firm Robinson Insight.



