
ISRAEL AT WAR
Israel’s security bodies receive direct access to biometric databases and cameras
In expedited legislation last week, the Knesset approved full access to the biometric database to the IDF, the police, the Shin Bet, and the Mossad. In a legal memorandum prepared by the government, it also seeks to grant them access to private security cameras and change the content of their recordings.
Israel’s police and security agencies will now be able to create a derivative of the national biometric database without adequate supervision and protection mechanisms, the IDF and the Shin Bet will be able to penetrate private security cameras without the need for court approval and without a mechanism to prevent the misuse of information. In addition, the cyber system and the Shin Bet will be able to order private businesses to carry out various actions in response to a cyber attack. Against the backdrop of the war with Hamas and in the name of real security needs, the government ministries have promoted and approved a series of laws, memoranda of law, and emergency regulations that threaten to change consolidated orders in a way that can harm the privacy and protection of information of all of us. Some of them may create irreversible situations, and all this without proper supervision by the judiciary or the Knesset.
The first move deals with the national biometric database, where facial images, and in some cases also fingerprints, of approximately 7 million Israelis are stored. On Wednesday, the Knesset approved in a second and third reading an amendment to the biometric database law that will allow the database data to be leveraged to help identify murdered, kidnapped, and missing persons. The law was approved in an expedited procedure only a week after the law memorandum on the subject was published to the public. The speed is jarring in light of the many years it took to enact and operate the database.
1 View gallery
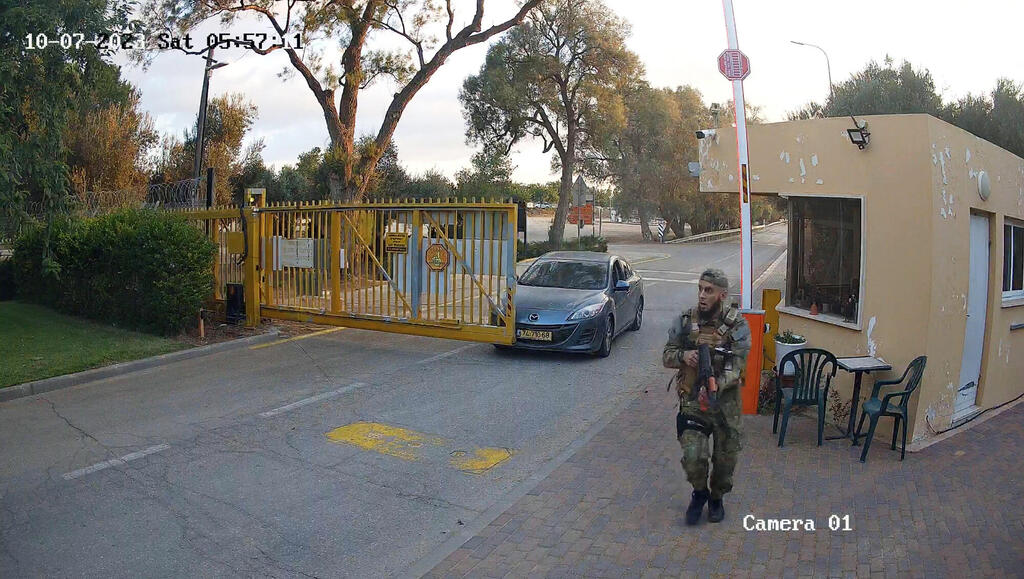
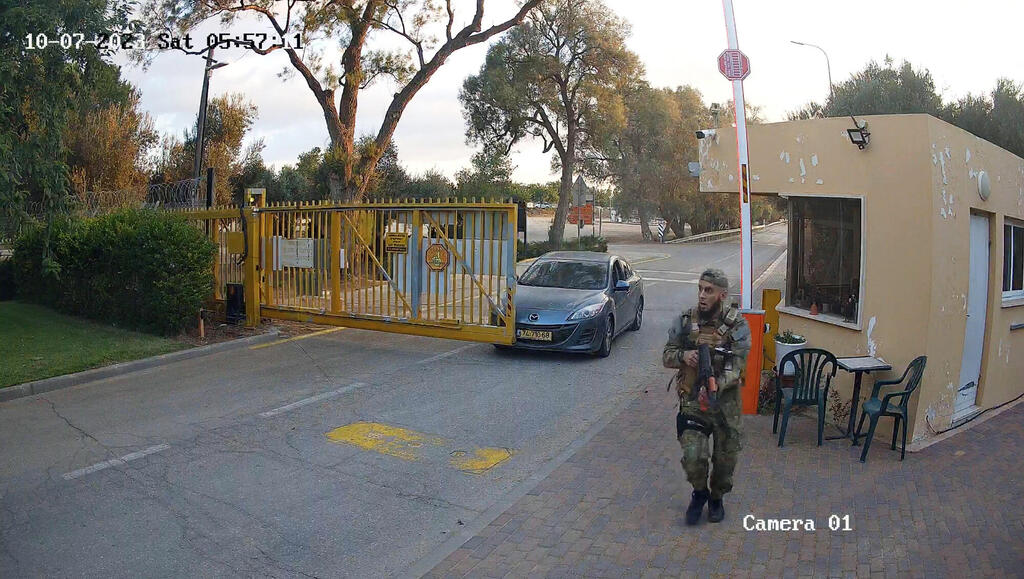
CCTV footage showing Hamas terrorists in Kibbutz Beeri on October 7
(Photo: South First Responders via Telegram)
The explanatory notes to the memorandum of law described an urgent need to change these procedures. "In view of the lack of a full response to the needs of identification in the police and IDF databases, an essential and urgent need has arisen for the possibility of transferring information from the biometric database in the Ministry of the Interior to both the police, and the General Security Service, the Intelligence and Special Task Force, and the IDF, for the purpose of identifying the murdered, the missing, the unknown, and the captives, as well as allowing the police to receive information from other sources," it said.
Emergency regulations from the first week of the war allowed the biometric authority to transfer biometric data to the security bodies for the purpose of verifying or clarifying a person's identity, "as much as they are required as a result of the events in which a special situation was declared on the home front." The legal memorandum sought to regulate the issue as part of a one-year temporary order.
According to the amendment to the law, at the request of the police, the Authority for the Management of the Biometric Database will provide them with means or biometric data that are necessary to verify or ascertain the identity of a person, living or dead, in the context of the war. This is a fundamental change in the way the biometric database works, since according to the law that regulates its activity, the data itself is kept in the database only and it is authorized to give the police only identification results (that is, the police can transfer a facial image or fingerprints to the database, and receive information about their suitability, but cannot receive the biometric data itself).
The law also makes another change in the way the database operates and states that the fingerprints, which only a year ago were determined to no longer be added to the biometric database, will actually be kept from now until the expiration of the temporary order. This is a change that returns to the database information that it was decided is no longer necessary for its current functioning for its main purpose (verifying a person's identity), and that its contribution to identification will be zero (the number of citizens who will submit their fingerprints to the database in the coming year and then it will also be necessary to identify them using them will surely be marginal).
More worrisome is the permission to extract data from the database, which will actually lead to the creation of a kind of new biometric database, but without all the protections and precautions that currently exist around the national biometric database. In this context, there is a concern that even after the temporary order expires, the data will not be deleted from the new biometric database, and in fact another permanent biometric database will be created, this time in the hands of the police, who can use it without adequate supervision.
"During the discussion, it was made clear that the security authorities are interested in making the law a permanent law in the future,” Zvi Dvir from the Movement for Digital Rights told Calcalist. “The decision that during the period of the temporary order, fingerprints of citizens renewing biometric documentation will not be deleted proves the true purpose of the law. The data is not used for the biometrics of citizens who come to the population office for the stated purposes of the law. Therefore, the hidden purpose of the law, which is no longer so hidden, is to reverse past decisions, according to which the biometric database will be based on facial images only, and that the fingerprint data will be deleted from it. In the words of the explanation, it is stated that 'according to the data of the Biometric Database Authority, the current situation resulted in the deletion of approximately one million fingerprints from the database in the last year'. The goal of the law is to stop the process of emptying the database, and to suppress the hidden purpose behind the terrible tragedy of the families of the kidnapped and missing."
The second move is a memorandum of law promoted by the Ministry of Defense, which seeks to give the IDF and Shin Bet the ability to access, retrieve, and delete information from private security cameras that are connected to the network. Access to these cameras is often not secure enough (there is no access password or the manufacturer's default password has not been changed), and often they overlook public areas or sensitive facilities and can be used by the enemy to gather intelligence.
The memorandum, which is intended to legislate emergency regulations that were approved in the first two weeks of the war, will allow a qualified officer to authorize an IDF soldier to break into a computer that is used to operate a stationary camera and to perform actions such as deleting, changing, or disrupting the visual information collected by the camera if there is any information to endanger the security of the state or the operational activity of the army, and the action is required in an "immediate and urgent" manner. The law allows this operation to be carried out even without the knowledge of the owner of the computer material, and without the need to obtain a court order. A similar authority is granted to the Shin Bet, which can also receive information from communications between computers without it being considered wiretapping. According to the memorandum, the law will be in effect for six months, when the Minister of Defense, with the consent of the Prime Minister and the approval of the Foreign Affairs and Defense Committee, may extend it for up to six additional months.
Although this is a vital need, the lack of oversight mechanisms is a significant cause for concern. The procedure is done without any need to obtain a court order, or even retrospective supervision by the court. There are no mechanisms in the memorandum to ensure that this authority will not be misused (for example, to track people) or to protect the security of information or the privacy of information that will be retrieved, except for the statement that "the IDF and the Shin Bet will not use or retain information, including knowledge of private affairs of a person."
Supervision on the part of the Knesset and the government is also extremely limited and amounts to a monthly report to the Foreign Affairs and Security Committee and the Attorney General on the number of soldiers or service workers who are authorized to carry out intrusion operations and the number of computers against which operations were carried out as well as the types of activity. The reports themselves will be confidential.
Along with these two memos, the government is also formulating emergency regulations that will expand the powers of the National Cyber Directorate and give it the authority to issue binding instructions to certain businesses in the event of a cyberattack. According to the draft regulations, which were revealed last week in Calcalist, the Cyber Directorate, the Shin Bet or Director of Security of the Defense Establishment has the authority to issue binding instructions to certain computer service providers in the event of a cyber attack. In addition, the provider of these services will be obligated to report a cyberattack within four hours at the most from the moment it is detected.
The Cyber Directorate explained that the regulations were not intended to replace the cyber law and that they only apply to one sector. However, privacy experts have warned that the choice of granting this authority by means of law and not in primary legislation is wrong since this is a broader arrangement in relation to other emergency regulations laws that have been passed since the beginning of the war, and that there is no reason not to resort to primary legislation since the Knesset is functioning. In addition, the wording of the regulations gives them a very broad applicability and they may apply to a large number of businesses. The reporting obligation contained in these regulations is very broad and may create a burden on the Cyber Directorate which will be flooded with requests that it will have difficulty dealing with.













